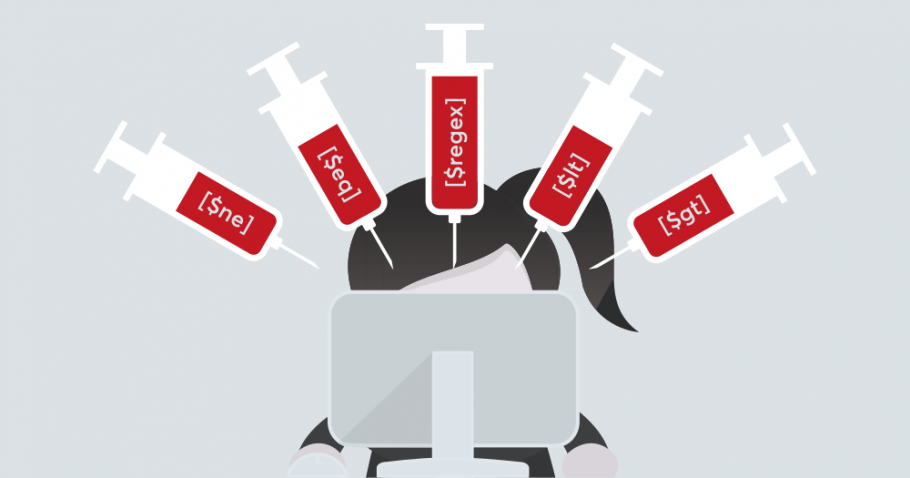
Insecure Mobile App Storage – Sensitive Data Stored in Plaintext on Devices
Introduction Mobile applications handle vast amounts of sensitive data, including personal information, financial details, and authentication credentials. However, many apps fail to implement proper security measures, leading to insecure mobile app storage, where critical data is stored in plaintext on devices. This negligence exposes users to severe risks, including data breaches, identity theft, and financial fraud….